Box Account Takeover Protection

Extend Abnormal Protection Across All Platforms
Cloud phishing breaches—that is, breaches affecting your cloud apps and services that result from the exploitation of human vulnerability through advanced phishing and social engineering tactics—are a primary concern for Security teams. When considering a breach, what target is more attractive than an organization’s primary file storage platform? Box is secure, but considering CISO’s concerns around storage app security, Box requires additional protections. To stop attackers from tearing open Box, security teams need an extensible platform that provides consistent visibility and security automation across not only Box but all cloud apps and services for holistic, higher-fidelity detection. Abnormal provides that platform.
How Abnormal Secures Box
Simple API Integration
Connect directly to Box with Abnormal’s cloud-native API architecture—automatically ingesting and normalizing sign-in signals related to every human in your organization that accesses the Box platform.
Continuous Monitoring of Human Behavior in Box
Build dynamic behavioral profiles for every human in your organization that uses Box, develop a behavioral baseline and automatically detect and analyze anomalous activities that deviate from that baseline.
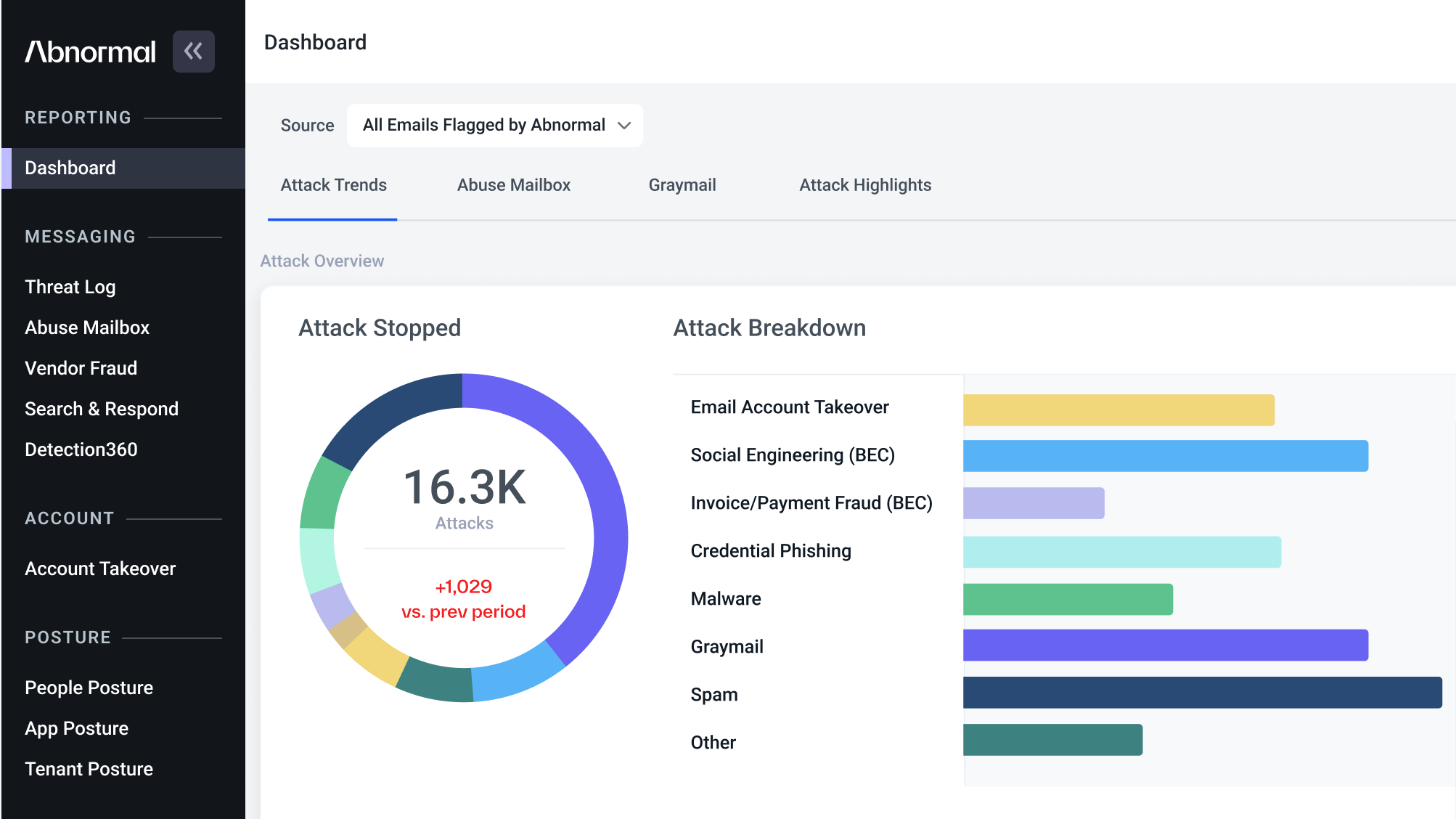
AI Account Takeover and Response
When suspicious activity occurs, Abnormal Human Behavior AI automatically triggers the creation of a contextual Case populated with Box activity. Each Case is scored based on detection confidence and continually enriched with new activity across all platforms integrated with Abnormal.
26%
of companies are targeted by account takeover attempts each week.
60%
chance of a successful account takeover each week for organizations with 50,000+ employees.
$329M
total amount saved by customers due to account takeovers stopped by Abnormal in 2023.
Get AI Protection for Your Human Interactions